Headline – Ethiopia is Asking Israel for assistance in its relentless battle with Al-Shabab from neighboring Somalia
Ethiopia is looking to Israel to help extricate itself from poverty and backwardness, that country’s ambassador Helawe Yosef Mengistu told The Jerusalem Post on the eve of Prime Minister Benjamin Netanyahu’s upcoming historic trip to Ethiopia. It is strategically looking to Israel for assistance in its war with the al-Qaida linked Al-Shabab from neighboring Somalia.
1 – Cooperation for National Security – Why Britain doesn’t play politics with gun tragedy
Ethiopia is Cameron stood shoulder-to-shoulder with Jeremy Corbyn, the Labour Leader of the Opposition, and with a bitter rival from his own party, Speaker of the Commons John Bercow, as the politicians laid bouquets in Cox’s memory.
It was a somber, awkward gathering, the swiftly arranged response of a political community unused to violence in its midst, particularly gun violence — least of all when it takes the life of an elected representative.
An ocean away — and only a few hours earlier — President Barack Obama and Vice President Joe Biden were also laying flowers in remembrance of victims of a gun attack. But there were no Republicans beside them in Orlando. Meanwhile Sen. John McCain — much respected in Britain, as well as America — was in Washington D.C. labeling President Obama “directly responsible” for Omar Mateen’s weekend massacre at the Pulse nightclub, on the basis that his foreign policy failures had inspired terrorism.
2- FALSELY REPORTED PROPAGANDA AGAINST SNA & FGS: 5,000 CHILD SOLDIERS INVOLVED IN AL-SHABAB CONFLICT, SAYS U.N. OFFICIAL
Regional Security experts have asked for fact checks of some of the falsely reported against SNA.
Black Propaganda gainst SNA: Some 5,000 child soldiers could be fighting in Somalia, according to a top UNICEF official, as both the Somali National Army and Al-Shabab utilize minors in a bloody conflict.
UNICEF Chief of Communication Susannah Price told Voice of America’s Somali service (Reported by Mohamad Olaad – Somali reporter) that Al-Shabab had stepped up a recruiting campaign aimed at children and that those living in camps for internally displaced persons (IDPs) as “an easy target.”
3- European Union has lifted the ban imposed on Sri Lanka’s seafood exports to the European Union with immediate effect
New Threat to Somali Tuna Industry and Waters: EU finalizes lifting the ban on Sri Lanka’s fish exports
The EU in April this year arrived at the decision to partially lift the ban following several rounds of discussions and decided to allow Sri Lanka to export fish within the next few months. The order to completely lift the ban was to be submitted to the European Parliament for approval. Earlier, Fisheries and Aquatic Resources Development Minister Mahinda Amaraweera predicted that documents pertaining to removal of the ban will be received by Sri Lanka in a late June.
Update: The government says Sri Lanka suffered $75 million (68 million euros) in lost revenue because of the ban, which was imposed in January 2015. Sri Lanka was a significant exporter of swordfish and tuna to countries in the EU
The Sri Lanka government suffered $75 million in lost revenue because of the Tuna ban. Sri Lanka was a significant exporter of swordfish and tuna to countries in the EU.
4- Good Lesson to be learn: Sri Lanka arrests four Indian fishermen for crossing maritime border
The fishermen had allegedly crossed the International Maritime Boundary Line and will be handed over to Sri Lanka’s Jaffna Fisheries Inspector.
At least four Indian fishermen were arrested by Sri Lankan Coast Guard with assistance from the Navy on Thursday for allegedly crossing the International Maritime Boundary Line (IMBL) and fishing in Lankan waters. The naval personnel arrested the fishermen along with an Indian fishing trawler on northwest of Delft Island
Update last Month: This is the second time that Lankan Navy has arrested Indian fishermen. The Navy assisted the repatriation of 34 Indian fishermen released from Sri Lankan custody yesterdy. They were handed over to the Indian Coast Guard Ship Sagar at the International Maritime Boundary Line (IMBL) North of Kankasanthurai. SLNS Ranavijaya and Coast Guard Craft “CG 48” were deployed for the mission.
5- U.S. Congress OKs Ongoing Cluster Bomb Sales to Saudi Arabia, Saying a Ban Would ‘Stigmatize’ the Weapons
Congress has opted to continue selling cluster bombs to Saudi Arabia, citing a need not to “stigmatize” the weapon. But human rights advocates pointed to the close vote, 216 to 204, as progress towards ending the U.S.-Saudi trade of cluster munitions, which advocates say causes indiscriminate carnage.
The House of Representatives voted Thursday against an amendment that would have blocked the transfer of American-made cluster munitions to Saudi Arabia.
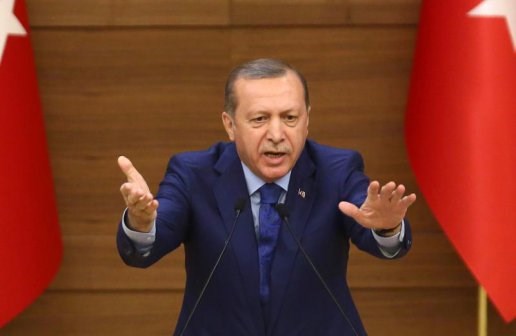
6- Inside Turkey: Turkey cancels Istanbul Gay pride due to ‘Security Fears’
Organisers describe ban as a “flagrant violation of the constitution” and say they will take legal action.
Government in Istanbul have banned transgender and gay pride marches this month, citing security concerns after ultra-nationalists warned they would not allow “degenerates” to hold the events on Turkish soil.
Update: A march in support of transgender people was planned for Sunday in central Istanbul, while an annual gay pride parade – described in the past as the biggest in the Muslim world – had been due to take place a week later on June 26.
“Degenerates will not be allowed to carry out their fantasies on this land … We’re not responsible for what will happen after this point,” he said, citing a Turkish proverb: “if you’re not taught by experience, you’re taught by a beating.”
7- As Russian Hackers Probe, NATO Has No Clear Cyberwar Strategy
In Estonia, there is widespread acknowledgment that the Western alliance has yet to develop a strategy to mitigate Russia’s increasingly aggressive actions in cyberspace. Outside of the frequent conferences and papers, there are no substantive military plans other than NATO locking down the alliance’s own networks. Russia, China, and Iran have increasingly sophisticated offensive cyberforces, but NATO has none. Moreover, it has no established mechanism to draw on the United States Cyber Command or its British equivalent. NATO’s action stands in stark contrast to its strategy for dealing with more familiar threats, such as the upcoming summit in July to deal with land invasions. NATO declared two years ago that it could rule a cyberattack on one of its member states to be the equivalent of an armed attack, which would lead to a commitment by all NATO members to respond. NATO commanders, however, do not seem prepared to aggressive countermeasures against the low-level probes, espionage, and attacks that go back and forth over European computer networks regularly. Jens Stoltenberg, the NATO secretary general, has taken a low-key, purely defensive view of what the alliance should do in cyberspace. According to James Lewis of the Center for Strategic and International Studies, the U.S. exhibits “a huge reluctance to share capabilities” with its NATO allies. “The Russians get that,” he says. “And they know that there is lots they can do without triggering any response.”
8- Pentagon Bug Bounty Contest Uncovers at Least 100 Vulnerabilities
More than 1,400 hackers participated in the Pentagon’s bug bounty program and found more than 100 security flaws, according to Defense Secretary Ash Carter. The 24-day program awarded $150,000 to hackers who found critical vulnerabilities and was the first government program of its kind. Carter said that the results “exceeded all of our expectations” and noted that the efficiency and decreased costs associated with the participating hackers was a massive success. HackerOne, a bounty program management firm that oversaw the proceedings, declined to provide information on the severity and types of vulnerabilities, but more details are expected later this week. Reports indicate that the Pentagon’s transparency during the program was an essential part of the overall success. One aspect of the program that is innately different from typical iterations is that the Pentagon made its program public. Most companies continue to keep bug bounty programs private. The Department of Defense has argued that such programs are a way to make good on the Cyber National Action Plan, a strategy document announced Feb. 9. The document mandates that the government prioritize immediate actions that improve the nation’s network defenses.
9- Belgium Downplays Report Terrorists En Route From Syria
Belgian authorities Wednesday downplayed security threats in the wake of reports that Islamic State fighters from Syria were making their way into the country. The security alert status will remain the same despite the warnings that fighters could have left 10 days ago for Belgium and France. The Derniere Heure reported that Belgium’s anti-terror office had been warned, though Brussels police said they had not seen any such warning from the anti-terror office. The paper said fighters traveling without passports were believed to be trying to reach Europe by boat via Turkey and Greece. A Brussels shopping mall, an American fast-food chain and police could be among their targets. The current threat level is three out of four, which signifies a threat is serious, possible, and probable. Belgium has been on level three or above since November following the Bataclan massacre that killed 130 people.
10- EgyptAir Flight 804 Wreckage Reported in Mediterranean
Searchers in the Mediterranean have found the first piece of sunken wreckage from the EgyptAir Flight 804 that crashed into the sea last month, the Egyptian government reported on June 15. News of the discovered wreckage was reported in a statement from the Egyptian Aircraft Accident Investigation Committee, which was established by the government to find out what happened to the plane. According to the statement, the search vessel, the John Lethbridge, had found and “identified several main locations of the wreckage” and that investigators had been provided with photographic images taken from the seabed, roughly 10,000 feet below the surface. The statement did not say whether the recovered pieces include the data recorders that are necessary to help determine why the plane crashed. The discovery is the first significant breakthrough in the search for the plane since investigators revealed they had picked up signals from one of its two flight recorder beacons almost two weeks ago. Air accident experts say that the distribution of the wreckage could yield crucial insight into what happened to the plane.
11-VTB Group CFO Aims to Bolster Cybersecurity Through Cooperation With U.S. Banks
Herbert Moos, finance chief of Russian state-controlled bank VTB Group, said cyberattacks on Russian banks are following similar trends as those in the United States. He said hackers are beginning to attack banks themselves, rather than clients, which is also happening in the American banking system. Earlier this year hackers attempted to use multiple compromised systems to overwhelm one of VTB’s systems in what is known as a distributed denial of service (DDoS) attack, Moos said. It was a shift in tactic, because the perpetrators launched a direct attack on the computer network of Russia’s second-biggest lender. Moos said he visited Silicon Valley recently to learn about cybersecurity efforts by U.S. banks, start-ups, and accelerators. VTB has invested in building its own private cloud and recently completed a disaster recover and redundancy site that backs up the bank’s computer systems “every second,” Moos said.
12- U.S. State Department Officials Call for Strikes Against Syria’s Assad
Dozens of State Department officials this week protested against U.S. policy in Syria, signing an internal document that calls for targeted military strikes against the Damascus government and urging regime change as the only way to defeat Islamic State. The “dissent channel cable” was reportedly signed by 51 State Department officers involved with advising on Syria policy in various capacities. The cable repeatedly calls for “targeted military strikes” against the Syrian government in light of the near-collapse of the ceasefire brokered earlier this year. The State Department acknowledged the existence of the letter, but would not comment until further review. The letter serves as an indictment of a longstanding U.S. policy against taking sides in the Syrian war, which has remained even after President Bashar al-Assad has repeatedly been accused of violating ceasefire agreements. Meanwhile, Obama administration officials have expressed concern that attacking the Assad regime could lead to a direct conflict with Russia and Iran. The letter could be a tactic to shape the foreign policy outlook of the next administration, some officials believe. According to the text, “Failure to stem Assad’s flagrant abuses will only bolster the ideological appeal of groups such as Daesh, even as they endure tactical setbacks on the battlefield.” The sentiment is echoed by leadership in Saudi Arabia and the UAE, which have pressed the U.S. to provide more advanced weapons to rebels to no avail.
13- Jo Cox Attack: UK Police Search for Motive Day After Lawmaker’s Killing
Investigators are still searching for a motive in the attack that killed British politician Jo Cox Thursday. Cox was stabbed and shot in Birstall after a meeting with constituents, and Tommy Mair has been arrested in connection with the case. While no motive has been suggested, Mair is believed to have connections to white supremacists. The murder has shocked Britain, a country with some of the world’s tightest gun regulations. Mair reportedly shouted “Britain first” before carrying out his attack, referencing the fringe nationalist political party that wants Britain to leave the EU. Weapons, including a firearm, were recovered at the scene of the killing, West Yorkshire police Chief Constable Dee Collins said. The party denied any involvement with the attack and said it would “never encourage behavior of this sort.” Cox was not with a security team since British lawmakers are so rarely considered to be at risk for assaults. Her death is hard on many of her constituents who praised her moral stances on tough issues. She championed for the rights of immigrants and campaigned against the exit from the EU.
14- CIA Director: Battlefield Advances Have Not Degraded ISIS’ Terrorism Potential
John Brennan, director of the Central Intelligence Agency, told the Senate Intelligence Committee on June 16 that the United States and its allies, while making progress on the battlefield against the Islamic State, “have not reduced the group’s terrorist capability and global reach.” He went on to say that the “resources needed for terrorism are very modest, and the group would have to suffer even heavier losses of territory, manpower, and money for its terrorist capacity to decline significantly.” He noted that the group has lost lots of ground in Iraq and Syria and that its finances have been tightened, but that it is also on the defensive now.
15- DHS Issues New Terror Warning After Orlando
The Obama administration issued a new official terrorism bulletin on June 15, cautioning against attacks from “homegrown” radicals. “In this environment, we are particularly concerned about homegrown violent extremists who could strike with little or no notice,” the Department of Homeland Security said. “The tragic events of Orlando several days ago reinforce this.” The notice is the second of its kind issued under a new federal terrorism notification system, which replaced the color-coded alert scheme used during the George W. Bush administration and a subsequent system that was never used. The first bulletin was issued after the attacks in Paris and San Bernardino, CA. A bulletin is the lowest in the three-tier system of notices about terror threats. The notice maintained that DHS does not have any “specific and credible” information that would suggest a terrorist attack inside the United States.
16- Most Companies Can’t Protect Confidential Documents
A majority of companies are unable to prevent employees from sharing confidential documents, according to a Fasoo study. Only 36 percent of more than 600 IT professionals surveyed say their companies are able to restrict document sharing between employees and third parties, and 27 percent of companies are able to restrict sharing between employees. Employees use free, consumer-grade file-sharing applications in 58 percent of companies, and 48 percent of respondents say employees are allowed to keep confidential files on their personal devices in some situations. Fasoo’s Ron Arden says companies are not aggressive enough in protecting their confidential documents, partly because of a lack of funding. “The CIOs would go to the board to get funding to plug the leaks, the board asks if there was a leak last year, the CIO says no, and they don’t fund it,” Arden says. The study also points to inadequate employee education about data loss prevention; 56 percent of companies do not educate employees about protecting documents. A Ponemon Institute survey found only 23 percent of companies conducted security audits of their confidential documents, and 69 percent of those who did found security issues.

Leave a Reply